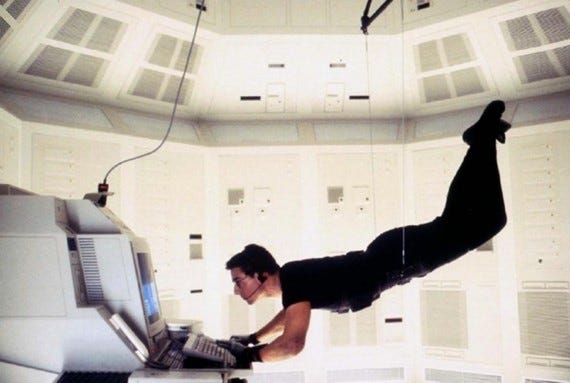
Sadly, intelligence breaches are more ‘Mission Inevitable’ than ‘Mission Impossible’
This week I found myself contemplating insider threats, inspired by news of the most serious US intelligence breach since Edward Snowden’s 2013 NSA revelations. The latest American leak is one of those stories where truth drags fiction into a pub carpark and gives it a sound thrashing.
So here’s my take on intelligence and security breaches from a policing perspective. Whether you’re a police or non-police reader, if you’re interested in operational security or social engineering, hopefully you’ll find something of interest. I’ve also steered away, as much as possible, from the strictly technical side of the business - I’m not a pen tester or computer forensics expert.
And so, to 21-year-old Jack Teixeria, a part-time reservist in the US Air National Guard (i.e. an air force part-timer). A low-ranking intelligence clerk, Jack enjoyed access to high-level intelligence reporting, which he shared on a social media platform popular with gamers. Why? It appears he simply wanted to show off.
Unsurprisingly, a member of his Discord group shared screenshots of the stuff Jack uploaded. Of course, it went viral in the nooks and corners of the internet popular with geeks, hackers, gamers and online investigators. There’s no evidence, to date, Jack was a spy, mole, whistle-blower or overly disillusioned with Uncle Sam. He was, in the sterile language of the insider threat industry ‘a careless / reckless employee.’
I’d say he was a puerile buffoon who shouldn’t have been given unsupervised access to the base lunch menu, let alone sensitive intelligence reporting. I’m old school like that. Most people who’ve worked with human sources realise the risk to individuals - and the integrity of the entire intelligence-gathering system - from deskbound idiots who can’t play by the rules.
In any case, Jack subsequently found himself bundled into the back of an armoured car by an FBI tactical team. A Supermax prison beckons.
Jack Teixeira: ‘Need to Know’ versus ‘Nice to Know’
Jack Teixeira’s story resonates with me, because at his age I was also a military reservist (in the British army Intelligence Corps). This was the very early 90s, before the Internet and 9/11. As a spectacularly unimportant lance corporal – analogous to Teixeira’s rank – I had access to very little sensitive material (nor any internet with which to share it). While serving in Germany in the early 90s I saw satellite images of Serbian artillery positions during the build-up to the Bosnian war. And that was about it.
Why wasn’t I given access to sensitive material? Because I didn’t need to know. There was a culture of security.
Fast forward to the 2020s, where low-ranking operators routinely enjoy access to top secret intelligence product, as did the-then Bradley Manning (now Chelsea Manning) back in 2010.
What changed between then and now?
Sure, an era of mass casualty terrorism and advances in information technology plays a significant part, but so do social, political and cultural factors. These are just as important as a shadowy guy in a hoodie ‘hacking the mainframe.’ After all, sources suggest 60% of known data breaches required a human asset inside the target organisation.
As usual, I’ll provide my bona fides for new readers. I spent much of my policing career working in and around intelligence environments, including before the 9/11 watershed. I held UK Developed Vetting status for 22 years, worked in Special Branch (which had an old-school and very un-policelike security culture) and STRAP environments (i.e. around communications intelligence). My work often involved handling CHIS (i.e. human intelligence sources). The unit I initially joined in the Met’s anticorruption command (the Intelligence Development Group, or IDG) was probably the nearest thing the Met had to an organic counterintelligence capability. I was trained as a CII (a covert internet investigator) and undertook in-depth social engineering training. During the News International investigation, I witnessed media ‘blagging’ first-hand, seeing how journalists and unscrupulous private detectives developed sources inside business, the public sector and government. I also, during my time on special branch, helped investigate several naughty intelligence officers from MI5 and MI6.
I’m reasonably qualified to comment on what a real-world ‘Insider Threat’ looks like, and how he or she operates.
An entire industry has grown up around insider threat - sadly for good reason
The Threat
As any security professional will tell you, insider threat looks like anyone working for (or with) your organisation. Any organisation - and I mean any - is vulnerable. As I write, there’s probably a Women’s Institute being infiltrated by hostile actors from a neighbouring village, tasked with identifying the secret ingredient in their award-winning marmalade. And a memo to anyone sharing Jack Teixeira’s prison cell: don’t tell him anything.
During my police service I encountered all of the people shown in the image above. DPS investigated jaw-dropping intelligence breaches - the young female officer sitting in a police car with her gang member boyfriend, monitoring her radio while his friends committed crimes. An officer caught on covert cameras using his phone to photograph intelligence reports. Staff accessing custody imaging to find pictures of celebrities. Others printing the criminal records of neighbours or their ex-partner’s new boyfriend. A Pc monitoring football intelligence logs to warn his hooligan mates of police activity on match days. There was even a detective misusing intelligence systems to monitor an ex-boyfriend with a lengthy criminal record - she lied about her association with him on a vetting form and wanted to know what he was up to.
This, by the way, was the small fry.
There was the force who discovered an inside agent planted inside their intelligence unit by an organised crime group. The Met detective in a relationship with a drug dealer, with who they shared sensitive tactical advice. The staff member with access to forensic databases, warning high-level heroin dealers they’d been identified via DNA and fingerprint evidence.
Incidentally, a consistent threat profile I saw was female police staff (not necessarily officers) with access to information systems. These employees were targeted by criminals using not especially subtle social engineering tactics and tasked with obtaining information. They would be taken to nightclubs in flash cars, romanced and be provided with a partying, Instagram-friendly lifestyle (note to internal investigators - social media is your friend).
It’s occasionally possible to profile other threat factors. In the Met, as I’ve written before, we saw (1) poorly-performing officers with (2) debts and (3) significant attendance management issues repeatedly coming to our attention. I’d also say (4) people with inappropriate relationships outside of the workplace. Sadly, managing these issues ties into issues of workplace culture, which I’ll discuss later. It’s also another reason why police forces should love and cherish their sergeants - line managers are your frontline against insider threat.
You see, it’s easier to hack a person than a computer network. And, in any case, you’ll most likely need a human to do that too. If you haven’t already, check out Jenny Radcliffe. Back in the day she’d have been my worst nightmare. Now I’m out of all that? I’d love to meet her.
So consider this; if this is possible in a police service - an organisation with dedicated operational security processes - how bad do you think things are in the private sector? Talking with industry professionals, I’ve heard how security is too often an afterthought. I saw industrial-scale credit card fraud in retail written off as a routine cost of business (“we pay poor wages, some of our staff join to steal and the company won’t shell out for CCTV covering card transactions,” a security manager told me). Don’t even get me started on the mobile telephone industry. I’ve seen how cheap it is to obtain call data from unscrupulous staff.
Then private industry complain police don’t do enough to counter fraud (which, to be fair, they don’t). Nonetheless, physician, heal thyself. But they don’t, possibly because the bottom line trumps the cost of security. I wonder if some executives would rather mitigate a data breach than prevent one - which would be far more expensive in the short term. Gotta meet those quarterly figures. Let’s call it ‘risk management’, shall we?
Police response to Insider Threat
Police officers use the term ‘commodity’ for anything a criminal might use to turn a profit (guns, narcotics, stolen goods). In the case of insider threats, the commodity is information. That is to say, intangible. Zeroes-and-ones. DPS investigators are occasionally (and understandably) leery of information leakage cases because juries find them problematic. People used to watching TV programmes, ones where cops enjoy access to all sorts of information at the touch of a button, often struggle with the intricacies of information security and user access levels. And, like fraud cases, sentences are usually modest compared to the damage done.
Juries often struggle with the intricacies of computer misuse legislation
The Met has a number of strategies to manage such threats, although during my time this was never particularly joined-up (quel surprise!). DPS coexisted with Operational Security (OpSy) and Vetting departments. Then there was SO15 (counterterrorism) which ‘owned’ the Met’s liaison with the security services and were responsible for national security investigations like breaches of the Official Secrets Act. None of them spoke much to the others, unless they were trying to unload a problem.
Call me a Martin Luther-type heretic, but I’d set up a dedicated Insider Threat unit. I’d make it part of a wider counterintelligence and security department. I might even call the whole thing ‘Special Branch’.
Compounding the problem, As I’ve written before on Substack, is ‘Adler’s Police Discipline Vortex’, whereby nobody knows exactly what misdemeanour fits where. If someone’s a suspected insider threat, what’s the way forward? Are they a criminal? A misconduct matter? A performance or organisational learning issue? An opportunity for a counterintelligence operation? All, some, or none of them? The answer was usually what was most convenient to any given decision-maker on any given day.
Nonetheless, the Met did have proper information security processes, the effectiveness of which increased the higher up the intelligence food-chain one travelled. For example, the Met Confidential Unit I retired from had solid STRAP compliance (you aren’t, for example, allowed mobile telephones in a STRAP accredited office). There was a dedicated STRAPSO (the person in charge of security) who knew his stuff and dealt with breaches proportionately and with good humour. And in Special Branch back in the day? Printer sweeps for documents. Clear-desk policies. Checks the safes were always locked. Proper old-school bollockings for breaches. It was strict.
Towards the end of my service, I worked with most police intelligence systems outside of counterterrorism - my bread-and-butter was the PNC, the Met’s Memex-based CRIMINT Plus (criminal intelligence) system, a tool called IIP (Integrated Intelligence Platform, which searched across multiple databases in the grandly-titled ‘Corporate Data Warehouse’) and the Police National Database (PND - clunky, but a genuine gamechanger, allowing officers to access data from other police services). There was a wealth of sensitive information at my fingertips - an insider threat’s dream.
Crucially, all of these systems were auditable. Too many systems don’t have audit built into their architecture - does yours? Audit means an administrator can interrogate systems to identify patterns of misuse. My old DPS team used a number of successful systems audit strategies to identify offenders. We also ‘corruption-proofed’ operations, covertly flagging intelligence to protect data against inappropriate access. I’m not going to say how that worked, but it was fun (well it was for me, I’m a bit of a geek).
If you’re a wrong ‘un inside the Job and you’ve attracted that level of scrutiny, I hope you’re sweating. Because there’s a good chance you’ll get caught - not least because we can audit CRIMINT back to 1996. It never forgets that moody check you did a few years back.
So don’t do it.
Nonetheless, given the sheer amount of data the Met processes - and the number of end-users - DPS couldn’t possibly identify every instance of inappropriate use. We required a culture where local systems administrators dip-sampled and analysed employee systems use - and that was a problem. On my CRIMINT systems administrator’s course, instructors and students acknowledged the level of audit was woeful. Why? Time, the amount of administration required and the discomfort of challenging colleagues about systems use were cited as reasons.
I don’t buy it. There should be NO discomfort about being asked about systems use. As a source-handler, I saw intrusive supervision as a tool to protect my interests, not to snoop or accuse. The stakes are simply too high.
This is, of course, a cultural issue. Which is the crux of the matter.
Systems admins and security professionals shouldn’t be treated like pesky traffic wardens, unless they choose to behave like one; effective compliance requires people skills as much as technical ability
Vetting and Culture
9/11 changed everything. If you’ve read the 9/11 Commission Report (and if you haven’t, I’d suggest it’s essential reading for any intelligence and security professional) you’ll understand why western security agencies swore to never again miss opportunities to prevent mass casualty terrorism. This meant dismantling empires, knocking heads together and ‘daring to share’ intelligence. Sadly, I think they ended up establishing a load more empires, but hey.
Intelligence, the Commission decided, was there to be shared widely. Used. Exploited.
Now, over twenty years later, I’ll ask the question; has the pendulum swung too far the other way? How much intelligence leakage is now acceptable under the ‘Dare to Share’ ethos? The social media landscape is completely different to that of 2001. Perhaps this is more of a question for our American friends, who seem to have decided a mass info-dump of caveated material across vast swathes of government is the way forward. I read somewhere the US parks service has the same level of access as Jack Teixeira. Were I leading a group of Jihadi otters, I suppose I’d be worried.
Luckily, the UK’s security and law enforcement agencies are more conservative. Nonetheless, many senior police officers, some of whom never served in intelligence roles, are innately suspicious of ‘need to know’ (especially those who’ve never held Developed Vetting status). This might be why cultural change is difficult - I saw far too many STRAP breaches committed by officers of superintendent level and above. The wannabe Jack Bauer-types one occasionally finds in SO15 were notable offenders - ‘reckless employees’, with a dysfunctional understanding of the relationship between rank, role, status and compliance.
An SO15 superintendent doesn’t realise his unauthorised use of a non-secure telephone just caused a helicopter to explode
A workplace culture where obvious employee red flags are noted, managers lead by example and transparency in systems use is normalised is one where you’ve already begun to mitigate the most common insider threats.
So is hiring the right people in the first place. Seems obvious, doesn’t it?
Which brings me to Vetting.
Vetting is unglamorous, unloved, occasionally expensive and probably one of the most effective tools an organisation has to protect itself from insider threats. I can personally attest to the nightmares resulting from hiring unsuitable people. After many expensive and resource-intensive investigations, we’d ask ourselves why our target was even hired in the first place. The red flags were usually there.
Outside Europe, and especially in Asia, businesses are more robust. They use fairly intrusive candidate screening to choose employees and establish their credentials. At this point, I’ll credit an old friend who’s influenced my thinking on the subject over the years, Mike Short. Mike, a former Royal Hong Kong Police detective, is a veteran of the risk management business with a focus on screening. We’ve often discussed insider threats in policing and business contexts, finding spookily familiar commonalities despite obvious cultural differences between Europe and Asia. This stuff, we concluded, is universal.
Another issue is human change. The person you hired three years ago is a different person now. Maybe they’re badly in debt. Do they feel bullied by their line managers? Perhaps there are performance or attendance problems?
And this employee has legitimate access to your most sensitive commercial databases as part of their role.
Who in the workplace knows any of this?
I’m not suggesting you spy on your workforce. I am suggesting line managers have both a welfare role and professional responsibility to identify potential problems and misconduct. Think about that discreet but crucial difference. Then again, and if it’s proportionate, a vetting or screening process might identify it too. Maybe some companies can’t be bothered to treat staff properly, or invest in a healthy security culture. There are plenty of sketchy, bottom-line, just-bought-out-by-a-hedge-fund outfits out there. Ones where bosses don’t really care.
Which brings me to my final point. I do wonder, when it comes to the subject of insider threats; do some businesses reap what they sow? I’m not beholden to any business or organisation, so I’m quite comfortable putting it out there. The idea of a fish rotting from its head is a recurring theme of my writing. I’m quietly confident what’s true of the public sector is equally true of business.
Look after your people. Most of them will reciprocate. For the rest? That’s what security professionals are for.







Dom
Dom
Dom
.... ah you tired old dinosaur. Expecting people to do their jobs properly and behave like grown ups. Look at poor recently devoid of status deputy PM. Didn't say please or thank you loud enough to Lucian or Arabella, so he bullied them by actually having the temerity to tell them what to do. I mean, who does he think he is? Doesn't he know how vulnerable and fragile I'm feeling now?
Oh the other lot are no better. Brown threw as you know titanic temper tantrums which involved hurling things at people. Brown isn't a small man. He's a solid brute. I've stood next to him behind him and in front of him.
Another very senior lab Cabinet minister liked to put his hands on the bodies of female staff. On parts of their bodies that only mothers, lovers and trained medical staff should touch. The PM knew. They all knew. Yet greater needs and interests prevailed.
The hypocrisy reeks. Another good SB man, we both probably knew, who sadly is no longer with us, once said to me: " Both are as bad as each other. "
I recall Det Supts and above in Strap environment using mobile phone. They seemed to find it amusing. I'm reminded of now disgraced ACSO whose attitude to DV Vetting was " Just funking get it done." He and his acolytes actively conspired with likeminded in other gvt depts to rain down fire, misery and brimstone on those who deserved to be swept away for having the temerity to dare object to the rise of the new Empire.
To Hell and Connaught with all of them.
Very much on point! Too often, complacent or naive, managers fail to spot potential security threats among their staff.